

Perimeter Protection: 5 Reasons It’s Vital for Critical Infrastructure
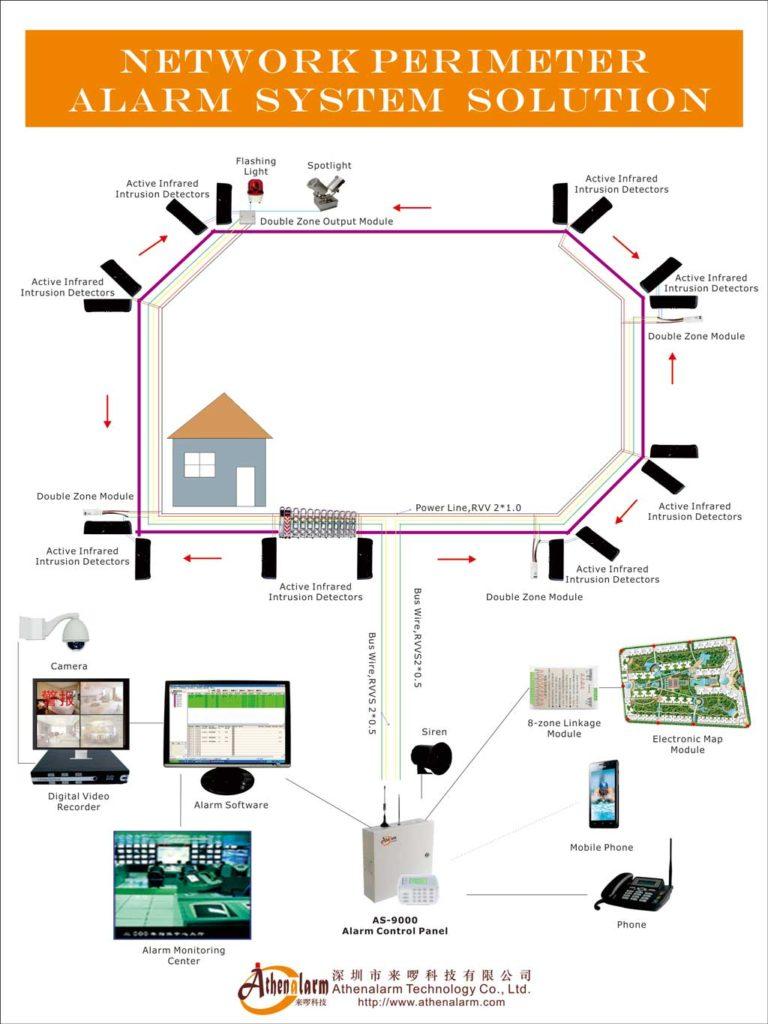
Table of Contents
1. Introduction
In a time of escalating threats—both physical and cyber—critical infrastructure facilities face unprecedented security challenges. Energy grids, airports, data centers, and water treatment plants are all prime targets for malicious actors ranging from petty trespassers to state-sponsored sabotage groups. The consequences of a successful intrusion could be catastrophic—disrupting public safety, damaging national assets, and triggering costly regulatory fallout.
2. Why Perimeter Protection Matters
Perimeter protection refers to the strategic application of surveillance, detection, and deterrence technologies to secure the physical boundaries of a facility. Unlike conventional security, which often relies on static guards or passive cameras, modern perimeter protection systems are intelligent, proactive, and fully integrated into command and control operations.
This layered approach is vital for high-value sites where early detection and rapid response can prevent escalation, reduce liability, and ensure business continuity.
3. Five Core Reasons Perimeter Protection Is Essential
3.1. Threat Detection and Recognition
Effective perimeter protection starts with visibility and awareness. Advanced systems enable early identification of suspicious activity—even under challenging environmental conditions.
Key Technologies:
- Thermal Imaging Cameras: Operate reliably in darkness, fog, smoke, or rain, identifying intruders by heat signatures.
- Ground Surveillance Radar (GSR): Detects motion beyond physical barriers, including in obstructed terrain.
- AI-Enhanced Video Analytics: Differentiates between real threats and environmental triggers such as animals or wind-blown objects, reducing false alarms.
- Thermal Virtual Fences: Crucial for remote areas or sites near water where traditional fencing is unfeasible.
Real-World Insight: A hydroelectric facility near a riverbank deployed radar and thermal cameras to monitor terrain inaccessible to patrols, catching multiple intrusion attempts months before they reached secure zones.
3.2. Automated Response Systems
Manual intervention is often too slow to neutralize fast-moving threats. That’s where automation steps in—executing deterrent actions within seconds of detection.
System Capabilities:
- Slew-to-Cue PTZ Cameras: Automatically turn to track motion, providing visual verification in real time.
- Trigger-Based Floodlights and Sirens: Act as immediate deterrents, signaling the intruder that they’ve been spotted.
- Intelligent Alerts: Metadata-rich, geo-tagged alerts are pushed to operators, enabling prompt action with full context.
Operational Benefit: Automation bridges the gap between detection and decision-making, enhancing responsiveness during multi-site incidents or during off-peak hours.
3.3. Real-Time Engagement for Deterrence
In many cases, the mere awareness of being observed is enough to stop an intruder. Real-time audio engagement creates a psychological boundary that discourages escalation.
Features:
- Two-Way Audio Communication: Operators issue live verbal warnings such as “You are under surveillance—leave the premises now.”
- Pre-Recorded Voice Commands: Activated based on predefined behaviors or geo-fencing triggers.
- Remote Operator Access: Enables off-site personnel to intervene without delay.
Use Case: A high-security logistics hub used two-way speakers to deter nighttime prowlers, resulting in a 70% drop in after-hours perimeter breaches within 6 months.
3.4. Delay and Intervention Mechanisms
Not every intrusion can be prevented at the boundary. That’s why a delay strategy—giving responders time to act—is essential.
Integrated Functions:
- Automated Gate Lockdown: Breach-specific zones can be locked down instantly using access control platforms.
- Mobile Unit Synchronization: Real-time alerts direct on-site patrols or security drones to the breach location.
- Video-Backed Access Control: Ensures visual confirmation before any access is granted, reducing the risk of insider threats.
Strategic Insight: A modular, open-platform setup allows seamless communication between devices, future-proofing the system and avoiding vendor lock-in.
3.5. Evidence Collection and Intelligence Analysis
Detection is only part of the security equation. Documentation and analysis are critical for compliance, legal proceedings, and continual improvement.
Core Capabilities:
- HD Archival Footage: Supports detailed forensic reviews and legal evidence requirements.
- GIS Mapping: Offers spatial awareness by linking footage to physical site maps.
- Mobile Access: Allows field personnel to access live feeds and incident logs in real time.
- Biometric Data Logging: Facial recognition and voice capture bolster accountability and threat profiling.
Compliance Value: Data retention protocols can help meet industry standards (e.g., NERC, GDPR) and demonstrate due diligence in the event of an incident.
4. Best Practices for Implementation
For perimeter protection to be effective, organizations must design systems tailored to their threat landscape and operational complexity.
4.1 Recommendations:
- Conduct Threat Modeling: Identify plausible threat vectors and critical vulnerabilities.
- Use Hybrid Architectures: Combine sensors, analytics, and physical barriers for a truly layered defense.
- Prioritize Compliance: Align solutions with local and international standards (e.g., CISA, NIST).
- Train for Escalation: Ensure personnel are trained not just in operations, but in emergency response protocols.
5. Overcoming Common Deployment Challenges
| Challenge | Proven Solution |
| High False Alarm Rates | AI filtering + multisensor correlation |
| Harsh Environments | Thermal/radar systems resistant to weather |
| Remote Locations | Solar-powered devices + wireless mesh networks |
| Budget Constraints | Modular rollout with prioritized zones |
6. Conclusion
In the defense of critical infrastructure, perimeter protection is more than a security measure—it is a strategic imperative. By integrating detection, automation, deterrence, delay, and documentation into a cohesive system, organizations not only protect their assets but also ensure operational continuity and stakeholder confidence.
A well-designed perimeter security system doesn’t just react to threats—it anticipates them. In today’s evolving threat environment, that’s the difference between resilience and risk.
7. FAQ
What is perimeter protection in critical infrastructure?
Perimeter protection refers to the integration of surveillance, detection, and deterrence systems to secure a facility’s physical boundaries, especially in high-risk environments like energy, data, and transport sectors.
Why is perimeter protection more important today than before?
With increasing threats—both physical and cyber—critical infrastructure requires proactive, intelligent systems that detect and respond to breaches before they escalate.
What technologies are used in modern perimeter protection systems?
Key technologies include thermal imaging, radar, AI-based video analytics, automated deterrents, two-way audio, and access control integrations.
How does perimeter protection reduce false alarms?
AI-powered video analytics combined with radar or thermal sensors filter out non-threatening motion, significantly lowering false positives.
Can perimeter protection systems operate in extreme weather?
Yes. Advanced systems use thermal and radar technologies that function in fog, rain, snow, and darkness—conditions where optical cameras may fail.
What role does automation play in perimeter protection?
Automation enables real-time responses—like triggering alarms, turning cameras, or locking gates—without waiting for manual intervention.
Is perimeter protection scalable for small or remote sites?
Absolutely. Modular designs allow organizations to start small and expand over time, using solar power and wireless connectivity for off-grid locations.
How is compliance ensured with perimeter protection systems?
Systems can be configured to align with standards such as NERC CIP, GDPR, and CISA guidelines, with logging and documentation for audit trails.
How does perimeter protection support legal investigations?
High-definition video archiving, geospatial logs, and biometric data capture provide legally admissible evidence for security incidents.
What is the ROI of investing in perimeter protection?
While the upfront cost can be significant, the long-term ROI includes reduced incidents, lower liability, improved compliance, and higher operational uptime.
