

Intrusion Detection Systems for Data Center Security: A Comprehensive Guide
Data centers are the backbone of modern digital infrastructure, housing critical computing resources, enterprise systems, and vast amounts of sensitive data. As cyber and physical threats grow more sophisticated, securing these facilities is no longer optional—it’s essential.
While cybersecurity measures such as firewalls, encryption, and intrusion prevention systems (IPS) mitigate digital threats, physical security remains a crucial yet often overlooked aspect of data center protection. Unauthorized access, tampering, or sabotage can result in data breaches, service disruptions, financial losses, and reputational damage.
This guide explores the role of Intrusion Detection Systems (IDS) for data center security, covering essential components, advanced technologies, best practices, and implementation strategies.
1. Why Intrusion Detection Is Critical for Data Centers
Data centers are prime targets for cybercriminals, corporate espionage, and malicious insiders. A well-structured IDS acts as an early warning system, detecting, analyzing, and responding to security threats before they escalate.
Key Physical Security Threats to Data Centers
- Unauthorized Access – Hackers, competitors, or disgruntled employees attempting to breach restricted areas.
- Physical Tampering – Attackers disabling security systems, installing rogue devices, or sabotaging hardware.
- Insider Threats – Employees or contractors exploiting access privileges for theft or data manipulation.
- Social Engineering Attacks – Manipulating staff into granting unauthorized access.
- Tailgating & Piggybacking – Unauthorized individuals entering secure zones by following authorized personnel.
- Device Theft & Malicious Implants – Planting keyloggers, skimmers, or wireless sniffing devices for espionage.
Implementing a robust intrusion detection system for data center security ensures real-time monitoring, automated alerts, and rapid incident response, preventing costly breaches.
2. Core Components of an Effective Data Center IDS
A high-performance IDS integrates multiple security layers, forming a comprehensive defense system.
A. Perimeter Security
- Reinforced Fencing – Anti-climb barriers with vibration and pressure sensors.
- Access-Controlled Gates – RFID, biometric, or PIN-based entry systems.
- AI-Powered CCTV Surveillance – Motion tracking and facial recognition for automated threat detection.
B. Access Control & Authentication
- Biometric Verification – Fingerprint, iris scan, or facial recognition for secure entry.
- Multi-Factor Authentication (MFA) – Combining passwords, biometrics, and smart cards for enhanced security.
- Mantraps & Airlocks – Dual-door entry systems preventing unauthorized access.
C. Intrusion Detection Sensors
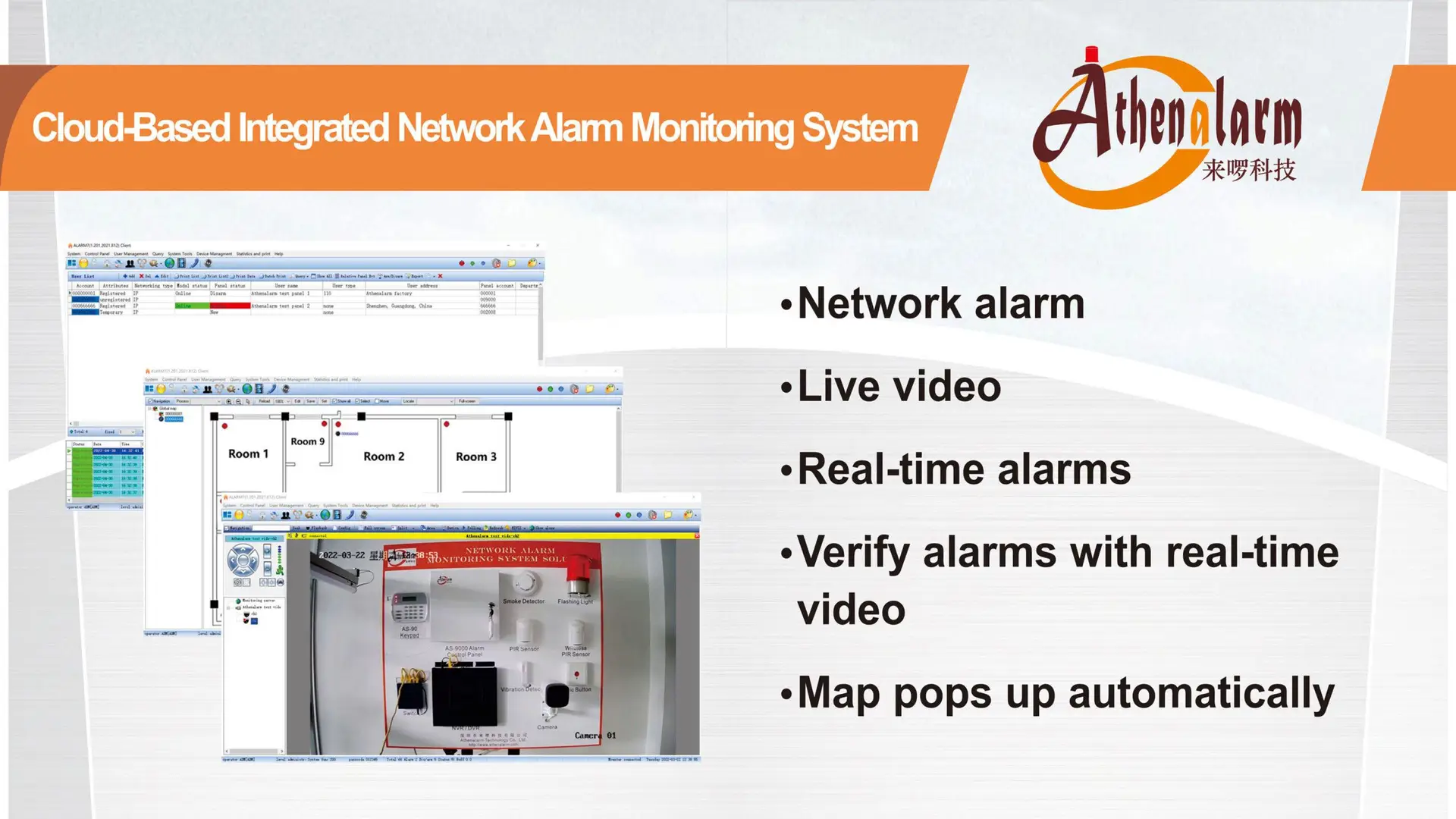
- Motion & Presence Detectors – PIR (Passive Infrared) and microwave sensors for movement tracking.
- Glass Break & Door Contact Sensors – Detecting forced entry attempts.
- Pressure Sensors – Identifying unauthorized access through floors or ceilings.
D. Alarm & Notification Systems
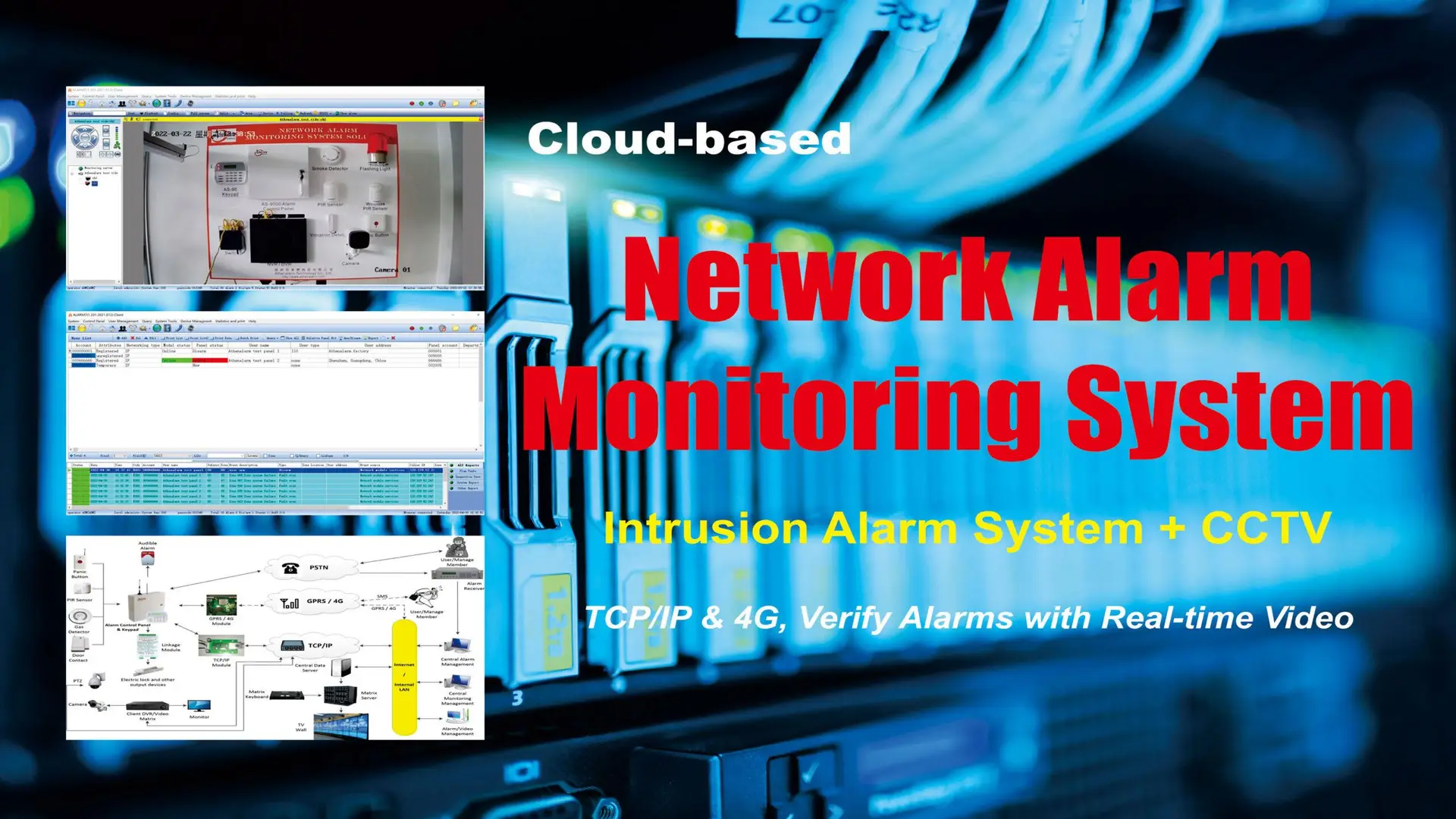
- Automated Alerts – SMS, email, or app notifications for security teams.
- Centralized Security Dashboard – Real-time IDS monitoring via a Security Operations Center (SOC).
- Integration with Law Enforcement – Direct emergency response connections.
E. AI & Machine Learning in Intrusion Detection
- Behavioral Anomaly Detection – AI-powered analysis of access patterns to identify suspicious activity.
- Automated Threat Response – AI-driven decision-making for lockdowns, alarms, and security alerts.
3. Implementing an Intrusion Detection System for Data Center Security
An IDS must be strategically implemented to maximize detection accuracy while minimizing false alarms. Follow this step-by-step approach:
Step 1: Conduct a Risk Assessment & Security Audit
- Identify vulnerabilities in perimeter security, access control, and surveillance systems.
- Analyze historical security incidents to pinpoint recurring threats.
- Define high-risk zones (e.g., server rooms, networking hubs, storage vaults).
Step 2: Select the Right IDS Components
- Choose appropriate sensors based on facility layout.
- Integrate AI-driven video analytics for real-time anomaly detection.
- Ensure seamless integration with cybersecurity frameworks.
Step 3: Configure Security Policies & Access Control
- Implement Role-Based Access Control (RBAC) to limit permissions.
- Enforce Multi-Factor Authentication (MFA) at all access points.
- Define incident escalation procedures for rapid response.
Step 4: Deploy & Test the IDS
- Install and configure physical security sensors and cameras.
- Conduct penetration testing to simulate breaches and refine the system.
- Adjust system sensitivity to minimize false alarms while ensuring real threat detection.
Step 5: Monitor, Maintain & Upgrade the IDS
- Implement 24/7 monitoring via an SOC.
- Regularly update AI-based algorithms to counter evolving threats.
- Conduct periodic security audits to ensure system reliability.
4. Advanced IDS Technologies for Future-Proof Security
A. AI-Enhanced Intrusion Detection
- Machine learning improves detection accuracy and reduces false positives.
- Predictive analytics anticipate threats before they escalate.
B. Biometric & Behavioral Access Control
- Continuous authentication using facial recognition and gait analysis.
- AI-driven anomaly detection for identifying suspicious access behaviors.
C. IoT & Edge Computing Integration
- IoT-connected sensors enable real-time perimeter monitoring.
- Edge computing processes security events locally, reducing latency.
D. Blockchain-Based Access Logging
- Immutable blockchain records provide tamper-proof logs.
- Ensures compliance with ISO 27001 and NIST 800-53 regulations.
E. Drone Surveillance for Perimeter Security
- Autonomous drones equipped with thermal imaging and facial recognition.
- Rapid response capability when an intrusion alarm is triggered.
5. Best Practices for IDS Maintenance
- Conduct Regular Security Drills – Train staff on incident response.
- Optimize False Alarm Reduction – Fine-tune system sensitivity.
- Integrate with Cybersecurity Frameworks – Unify physical and digital security.
- Establish Clear Incident Reporting Protocols – Define structured response plans.
- Adopt a Zero Trust Architecture – Continuously verify all access requests.
6. Conclusion
Securing data centers requires a multi-layered security strategy that integrates physical security, access control, AI-driven monitoring, and automated threat response. A robust Intrusion Detection System (IDS) for data center security is essential to mitigating risks such as unauthorized access, insider attacks, and hardware tampering.
By implementing advanced IDS technologies and following industry best practices, organizations can:
- Safeguard mission-critical infrastructure
- Ensure regulatory compliance
- Prevent costly security breaches
Investing in a comprehensive IDS strategy protects valuable data assets and reinforces an organization’s security resilience against evolving threats.
