

Maximizing Protection: Industrial Intrusion Detection Alarm Systems
In today’s fast-evolving industrial landscape, security is paramount for businesses managing valuable assets, sensitive data, and critical infrastructure. Facilities such as manufacturing plants, warehouses, power stations, and logistics centers face increasing threats, including theft, unauthorized access, industrial espionage, and cyber-physical attacks.
Industrial Intrusion Detection Alarm Systems (IIDAS) are essential for mitigating these risks by providing real-time alerts, integrating with security networks, and ensuring multi-layered protection. This article explores the key functions, components, advanced technologies, and best practices for deploying IIDAS effectively.
1. Understanding Industrial Intrusion Detection Alarm Systems
An Industrial Intrusion Detection Alarm System (IIDAS) is a sophisticated security solution designed to detect, alert, and respond to unauthorized access attempts in industrial environments. Unlike commercial or residential alarm systems, IIDAS solutions are built to withstand harsh environmental conditions, manage high-traffic areas, and integrate seamlessly with advanced security infrastructure.
A. Key Functions of IIDAS:
- Perimeter Protection – Monitors external boundaries, fences, and access gates.
- Intrusion Detection – Identifies unauthorized access to restricted zones.
- Real-Time Alerts – Immediately notifies security personnel and law enforcement.
- Access Control Integration – Works with authentication systems to manage entry permissions.
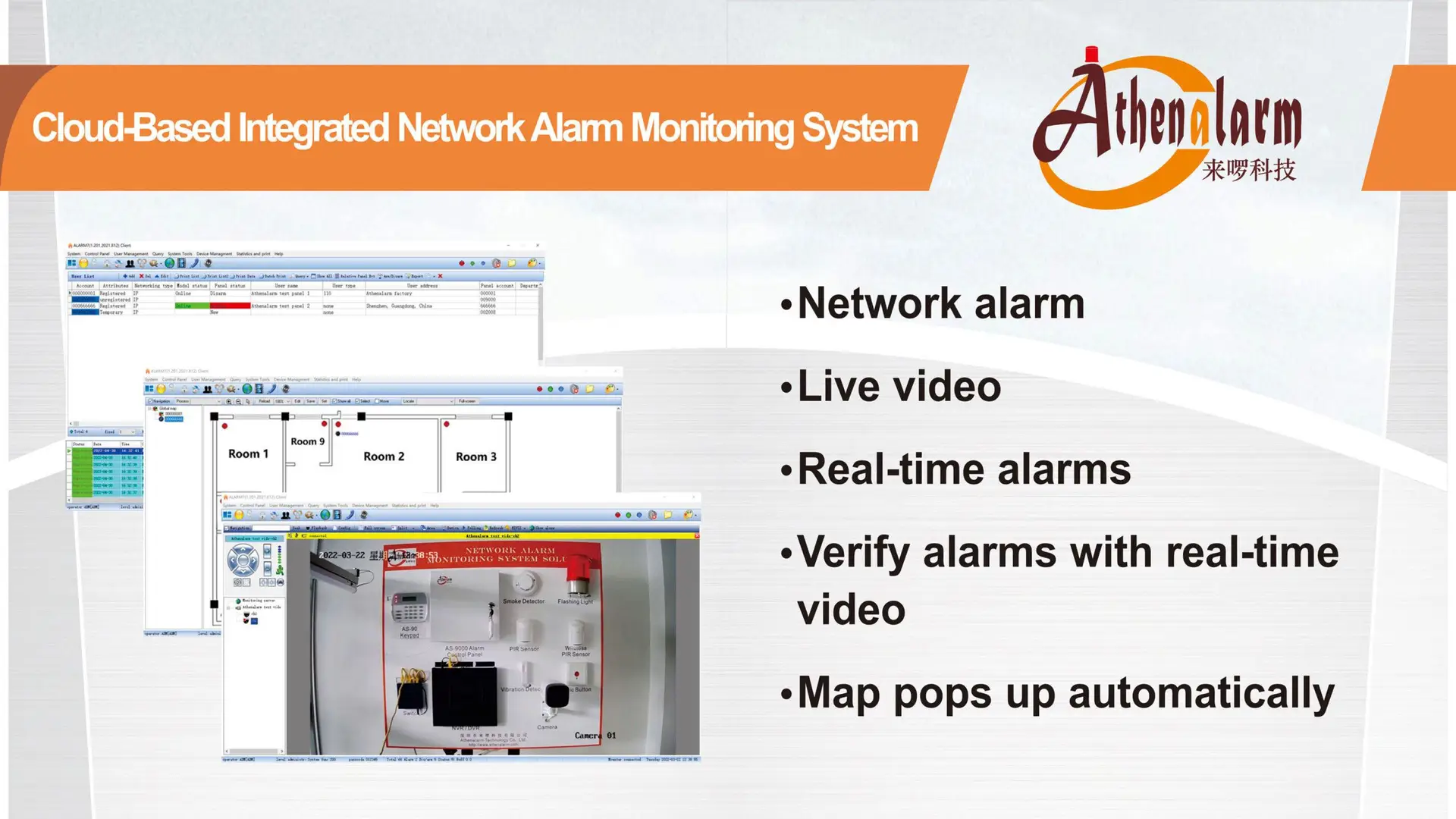
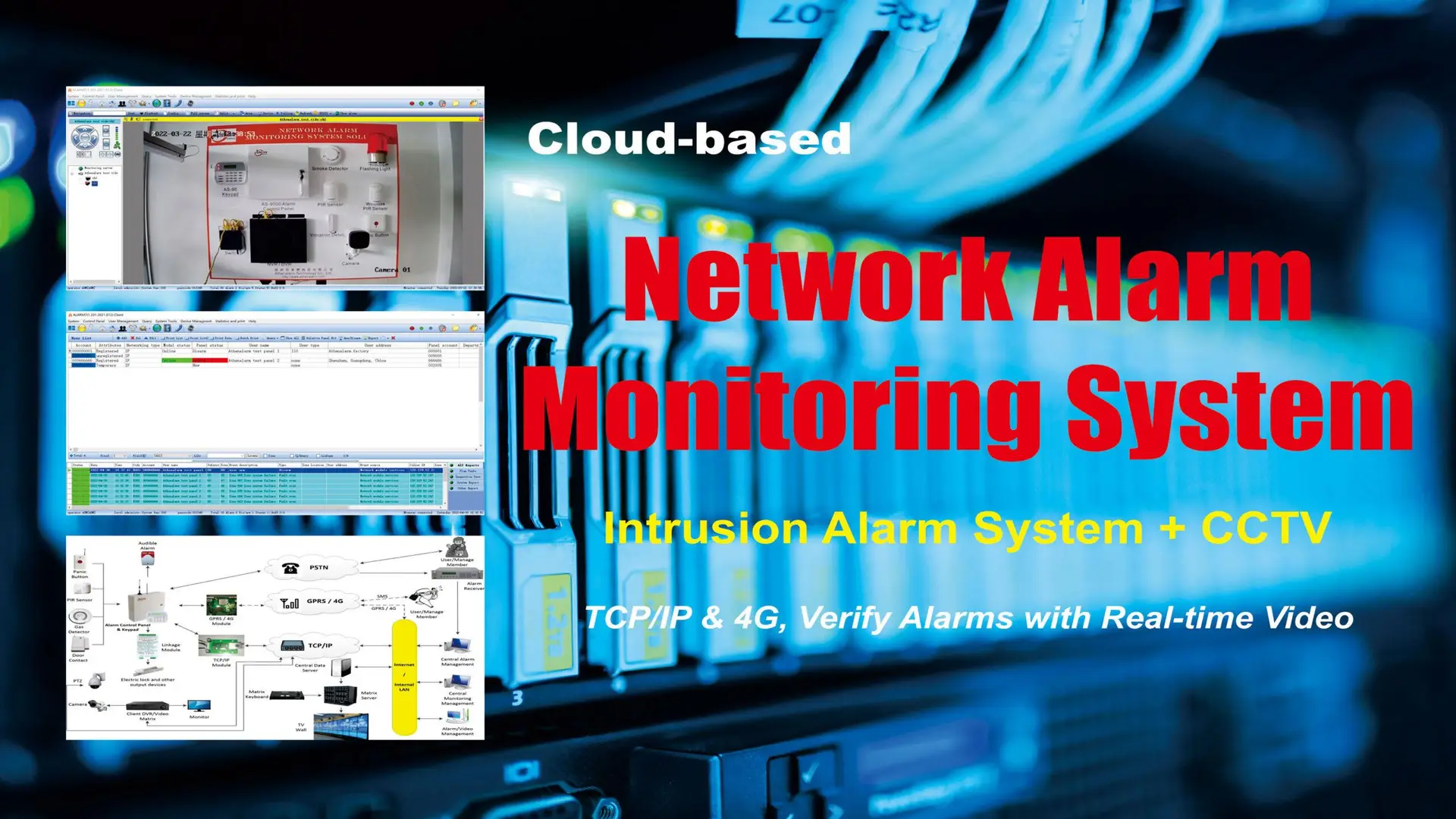
- Remote Monitoring & Automation – Enables centralized control and real-time security management.
B. Industry-Specific Applications:
- 1) Manufacturing Plants – Protects valuable machinery, intellectual property, and raw materials.
- 2) Warehouses & Logistics Centers – Monitors cargo movement, prevents inventory theft, and integrates with fleet tracking.
- 3) Energy & Utilities – Secures power plants, oil refineries, and water treatment facilities from sabotage.
- 4) Data Centers – Prevents cyber-physical attacks and unauthorized data breaches.
2. Core Components of Industrial Intrusion Detection Alarm Systems
A robust IIDAS consists of multiple hardware and software components designed to address specific security challenges.
A. Perimeter Intrusion Detection
- Fence-Mounted Sensors – Detects cutting, climbing, or vibrations on perimeter fences.
- Buried Pressure Sensors – Identifies movement near secured areas while remaining hidden.
- Infrared & Microwave Barriers – Creates invisible detection zones that trigger immediate alarms.
B. Motion Detection & Advanced Sensors
- Passive Infrared Sensors (PIR) – Detects body heat emitted by intruders.
- Radar-Based Motion Sensors – Provides reliable tracking even in adverse weather.
- Lidar & Laser Sensors – Offers high-precision movement tracking and object differentiation.
C. Video Surveillance & AI Analytics
- AI-Enabled CCTV Cameras – Identifies suspicious activities in real time.
- Thermal Imaging Cameras – Detects intruders even in complete darkness.
- Facial Recognition Systems – Enhances access control in high-security areas.
D. Alarm & Communication Systems
- Loud Audible Sirens & Strobe Lights – Deters intruders with visible and audible warnings.
- Cloud-Based Alerts – Sends notifications to mobile apps and control centers.
- Automated Law Enforcement Contact – Triggers emergency response upon confirmed threats.
3. Advanced Technologies Enhancing Industrial Security
Modern security technology has significantly enhanced IIDAS capabilities. Below are key innovations improving industrial security:
A. AI-Powered Anomaly Detection
Machine learning algorithms analyze movement patterns to differentiate between routine activities and genuine threats, reducing false alarms and improving response efficiency.
B. IoT & Smart Security Integration
IoT-connected sensors communicate with access control, fire suppression, and HVAC systems, creating a fully automated and interconnected security ecosystem.
C. Cybersecurity Measures for IIDAS
With rising cyber threats, IIDAS must be fortified against hacking attempts by:
- Implementing encrypted communication channels for alarm transmissions.
- Conducting regular firmware updates to patch vulnerabilities.
- Enforcing multi-factor authentication for system access.
D. 5G & Edge Computing for Instant Threat Response
5G technology enhances security system efficiency by enabling real-time data processing, minimizing latency, and accelerating threat response.
4. Best Practices for Deploying an Effective IIDAS
A well-implemented IIDAS requires strategic planning, execution, and continuous optimization.
A. Conduct a Security Risk Assessment
- Identify high-risk entry points using historical security incident data.
- Evaluate environmental factors that may affect sensor performance.
- Assess cyber-physical vulnerabilities to prevent hacking and sabotage.
B. Optimize Sensor and Camera Placement
- Position motion sensors at all access points and high-traffic areas.
- Utilize AI-driven video surveillance to minimize blind spots.
- Deploy thermal cameras in low-visibility zones.
C. Implement Multi-Layered Security Measures
- Integrate perimeter detection with AI video analytics for proactive security.
- Enable cloud-based monitoring for real-time oversight.
- Automate lockdown protocols in case of breaches.
D. Routine Maintenance & System Upgrades
- Regularly test sensors, alarms, and video analytics software.
- Update AI algorithms to adapt to emerging security threats.
- Train security personnel on interpreting system alerts and emergency response procedures.
E. Emergency Response & Law Enforcement Coordination
- Develop clear standard operating procedures (SOPs) for security breaches.
- Install panic buttons in high-risk areas for instant alerts.
- Integrate automated law enforcement notifications to expedite response times.
5. Future Trends in Industrial Intrusion Detection Systems
Advancements in technology and evolving security threats are shaping the future of IIDAS. Here are key trends driving change:
A. AI-Powered Predictive Security
AI-driven predictive analytics will identify potential threats before they occur, significantly reducing security risks.
B. Autonomous Security Drones & Robotics
AI-powered drones and robotic patrols will offer 24/7 autonomous surveillance, detecting anomalies in real time.
C. Blockchain-Based Security Authentication
Blockchain technology will enhance access control verification, making credentials tamper-proof and eliminating unauthorized duplication.
D. Quantum Encryption for Cybersecurity
As IIDAS becomes more connected to digital infrastructure, quantum encryption will offer an unbreakable layer of protection against cyber threats.
6. Conclusion
Industrial Intrusion Detection Alarm Systems (IIDAS) play a crucial role in safeguarding assets, ensuring operational continuity, and mitigating security threats. By leveraging advanced sensor technologies, AI-driven analytics, and multi-layered security strategies, businesses can significantly enhance their security posture.
Investing in a well-designed IIDAS minimizes financial losses, prevents operational disruptions, and creates a more secure industrial environment. As security threats evolve, staying ahead with cutting-edge solutions is essential for ensuring long-term protection for industrial assets and infrastructure.
